Allot ServiceProtector protects your data network against the increasing scale and complexity of inbound and outbound cyber attacks that are designed to flood your network and disrupt service availability. Mobile, fixed and cloud service providers around the world rely on Allot ServiceProtector to surgically mitigate volumetric DoS/DDoS attacks and neutralize IoT device anomalies and outbound threats before they are able to impact network service and business continuity.
Not Registered? Click here to sign up
-
Contact: +844-3766-3766
Cyber Security
Threat intelligence as a service is also a high-growth category, with 26% of organisations saying investment in this service is in their adoption plans. Threat intelligence has emerged as a means by which security professionals can finally proactively prepare for, and respond to, attacks. According to the survey, 63% of security decision-makers say establishing or improving threat intelligence capabilities is a top priority for their organisation. Being partner of PaloAlto Network and Allot, with vealuable experience in Cyber Security solutions, ISTT is proud to be a trusted tehnology partner of big operators in Vietnam.

Your First Line of Network Defense Against Cyber Threats
 Allot ServiceProtector helps you detect and surgically block Denial of Service (DoS/DDoS) attacks within seconds, before they are able to threaten or disrupt your network service. Allot inspects 100% of the traffic on your network to ensure that no threat goes undetected. Dynamic creation of filtering rules and surgical filtering of attack packets avoids over-blocking and allows legitimate traffic to flow unimpeded, keeping your business online and protected at all times.
Allot ServiceProtector helps you detect and surgically block Denial of Service (DoS/DDoS) attacks within seconds, before they are able to threaten or disrupt your network service. Allot inspects 100% of the traffic on your network to ensure that no threat goes undetected. Dynamic creation of filtering rules and surgical filtering of attack packets avoids over-blocking and allows legitimate traffic to flow unimpeded, keeping your business online and protected at all times.
 Allot ServiceProtector automatically detects and blocks outbound spam, worm propagation, and port scanning traffic generated by bot-infected users, so you can prevent DNS blacklisting and eliminate additional traffic load on your network. Allot identifies host infection and abusive behavior according to abnormal outbound connection activity and malicious connection patterns, enabling you to treat the root cause of the threat as well as the symptoms.
Allot ServiceProtector automatically detects and blocks outbound spam, worm propagation, and port scanning traffic generated by bot-infected users, so you can prevent DNS blacklisting and eliminate additional traffic load on your network. Allot identifies host infection and abusive behavior according to abnormal outbound connection activity and malicious connection patterns, enabling you to treat the root cause of the threat as well as the symptoms.

Allot ServiceProtector guards your network against IoT connected devices that are behaving abnormally, either through malfunction or misuse, and thereby causing unpredictable network congestion and denial of service. Allot employs multiple methods to detect anomalous connection behavior or traffic volumes and to block or limit access to misbehaving IoT devices in real-time, before network performance and availability are compromised. Allot also pinpoints the source of the anomalous behavior, so you can quickly remediate malfunctioning devices at their source, and prevent IoT devices from serving as a vehicles for cyber attacks. Real-time outlier alerts enable immediate and automated response to abnormal behavior from any device, providing the scalability and continuous maintenance you need to ensure that connected “things” are controlled without incurring the overhead of per-device access control, data validation or management client.

Security as a Service for Consumers
Allot WebSafe Personal is part of Allot’s leading Security as a Service offering for mobile and fixed networks, providing network-based parental controls and anti-malware services that enhance your brand and generate recurring revenue. Allot WebSafe Personal services are delivered from your network or cloud and therefore have no impact on device performance or battery life. Moreover, your customers enjoy uniform setup options for all devices and hassle-free maintenance.
Parental Controls provide peace of mind
Allot WebSafe Personal assures child-safe browsing and provides peace of mind by allowing parents to determine the websites and content that their children can access, as well as the hours and amount of time they spend online. Accurate web filtering techniques control access in real-time according to individual user profiles, which the parent manages online.
Anti-Malware protects personal devices
Allot’s network-based anti-malware service powered by Kaspersky Lab, Sophos and Bitdefender, protects customers against all kinds of malware that can damage mobile devices and cause the loss of personal content. The service also includes powerful anti-virus and anti-phishing for email (SMTP, POP3, IMAP) and web traffic, which takes the worry out of engaging in online activity and mobile transactions.

Palo Alto Networks was founded in 2005 by Nir Zuk, a former engineer from Check Point and NetScreen Technologies. Zuk served in the elite Unit 8200 of the Israel Defense Forces and, was the principal developer of the first stateful inspection firewall and the first intrusion prevention system. In 2009 Gartner, Inc. released a publication defining the “next-generation firewall”. In its definition, Palo Alto Networks firewalls contain application awareness, full stack visibility, extra-firewall intelligence, and upgrade paths in addition to the full capabilities of both traditional firewalls and intrusion prevention systems.
Palo Alto Networks is assessed as a Leader, mostly because of its NGFW focus, and because of its consistent visibility in Gartner shortlists for advanced firewalls use cases, frequently beating competition on feature quality
Palo Alto Networks next-generation firewalls are architected to safely enable applications and prevent modern threats. Our approach identifies all network traffic based on applications, users, content and devices, and lets you express your business policies in the form of easy-to-understand security rules.
Flexible deployment options and native integration with our next-generation platform extend the policy enforcement and cyberthreat prevention to everywhere your users and data are located: in your network, on your endpoints and in the cloud.
Palo Alto next-generation firewall classifies all traffic, including encrypted traffic, based on application, application function, user and content. You can create comprehensive, precise security policies, resulting in safe enablement of applications. This lets only authorized users run sanctioned applications, greatly reducing the surface area of cyber attacks across the organization.
 The Single-Pass Architecture is the overall design approach for our next-generation firewalls. The architecture enables full, contextual classification of traffic, followed by a rich set of enforcement and threat prevention options. The architecture classifies and controls traffic in a “single pass” through the firewall using a variety of stream-based technology components.
The Single-Pass Architecture is the overall design approach for our next-generation firewalls. The architecture enables full, contextual classification of traffic, followed by a rich set of enforcement and threat prevention options. The architecture classifies and controls traffic in a “single pass” through the firewall using a variety of stream-based technology components.
This architecture is unique in the industry, allowing you to achieve superior security posture and efficiency. Our next-generation firewalls are implementations of the single-pass architecture, available in a range of portfolio options (both physical and virtual).
The combination of Content-IDTM and WildFireTM provides protection from known and unknown threats. Content-ID limits unauthorized data transfer and detects and blocks a wide range of threats. WildFire identifies unknown malware, zero-day exploits, and advanced persistent threats (APTs) through static and dynamic analysis in a scalable, virtual environment, and automatically disseminates updated protections globally in near-real time.

Palo Alto Networks Traps replaces traditional antivirus with multi-method prevention, a proprietary combination of purpose-built malware and exploit prevention methods that protect users and endpoints from known and unknown threats. Traps prevents security breaches, in contrast to breach detection and incident response after critical assets have already been compromised.
Traps Advanced Endpoint Protection:
- Prevents cyber breaches by preemptively blocking known and unknown malware, exploits and zero-day threats.
- Protects and enables users to conduct their daily activities and use web-based technologies without concerns for known or unknown cyberthreats.
- Automates prevention by autonomously reprogramming itself using threat intelligence gained from WildFire.
Traffic Managament
Control Network Congestion and Application Performance
Data networks are not only carrying constantly growing volumes of Internet traffic and cloud services. They are also carrying different kinds of traffic that often strain them, making it much more complex to assure the performance of applications and services. For example, streaming video is data-intensive and user experience is highly sensitive to congestion and latency on the network. Likewise, as the Internet of Things (IoT) gains momentum, millions of new endpoints will be sending small amounts of data, whose impact on network performance is still unknown.
Making applications perform efficiently and consistently
Nobody likes to use a slow-moving application. That’s why Allot Traffic Management tools are designed to overcome today’s significant application challenges, enabling you to deliver a quality experience at all times, even when your network is at peak usage. Furthermore, Allot Traffic Management tools help you increases operational efficiency and ensure high-performance delivery of business-critical applications and services by dynamically regulating the bandwidth and Quality of Service (QoS) that your network allocates to every application and user.

Allot-Deep Packet Inspection
Dynamic Actionable Recognition Technology (DART) is our superior brand of Deep Packet Inspection (DPI) technology which is embedded in our high-performance platforms. Integrating our vast expertise in IP traffic identification and traffic classification, DART is at the core of our highly effective solutions for managing bandwidth utilization and application performance in any network. DART delivers the granular visibility that enables service providers to optimize and monetize their assets, and enterprises to control and secure their business-critical applications.
Clear benefits
- Granular visibility of all network traffic, including OTT applications
- Multi-dimentional insight into application, user, device, access, context, video and more
- Identification of thousands of applications and sub-applications in all network scenarios
DART delivers multi-dimensional awareness
- Applications: Identifies and accurately classifies more applications and protocols than any other solution, enabling any action – analysis, control, optimization – to be taken at the same level of granularity.
- Users: Identifies the users generating the traffic e.g., a user playing a game on a tablet, a user in a WhatsApp chat on an iPhone, and a user watching YouTube videos on an Android phone. Devices: Identifies the devices being used – dongle, smartphone, tablet – and the device manufacturer. This device awareness powers a myriad of use-cases including tethering identification, new device campaigns, device-aware optimization and more.
- Access: Provides access-aware visibility that allows the monitoring and control of traffic flows at specific access points in order to maintain network performance. Cell awareness in mobile access and CMTS awareness in cable access are two leading scenarios enabled by DART.
- Context: Identifies what users are doing in the application, and not just the application being used e.g., users can be watching a video, browsing, or chatting with friend on the same application. Such types of usage may relate to different use-cases with different user quality expectations.
- Video: Provides unique information about OTT video – including Quality of Experience parameters, video attributes such as resolution and format, and specific content details – enabling an in-depth view of video consumption and the overall quality of video delivery.

Bird’s Eye View of Your Network
As the scalable management system for our devices, platforms, and value added services, Allot NetXplorer gives you a central vantage point for network-wide policy management, traffic monitoring, and usage reporting. Its intuitive graphical interface paints a consolidated picture of application, user, device, and network topology traffic with easy drill-down to reveal the most granular network transactions and activities.
Providing the power to see and act
Allot NetXplorer supplies the network business intelligence essential for IP service optimization. It helps you understand how your bandwidth resources are being consumed by applications and users on the network, and defines traffic management policies that link service and performance parameters to your business goals and user expectations. With a full complement of real-time and long-term reporting capabilities, Allot NetXplorer provides unsurpassed visibility and control of your carrier, cloud or enterprise network. The fully distributed design of Allot NetXplorer is suitable for traditional and virtualized network environments, allowing the system to scale upward by adding functional elements at the appropriate architectural layers, while maintaining overall management from a central server.

Differentiate Your Service and Drive New Revenue
For broadband service providers, it’s all about providing differentiated consumer and enterprise cloud services that consistently deliver the Quality of Service (QoS) that each customer expects. For enterprises, it’s all about aligning application performance to business needs and increasing employee productivity. Allot Subscriber Management Platform (SMP) helps service providers and enterprises achieve these goals for any access network and any user. By leveraging Allot SMP’s application-aware, user-aware, and network-aware service tiering, policy control, and real-time charging, service providers and enterprises alike are able to differentiate their service offering and drive the user experience.
Creating more profitable service plans
Allot SMP makes it easy to deploy differentiated service plans or define cloud tenant SLAs, as well as accurately monitor and meter the consumption of network and cloud services per user, per service plan or SLA. Real-time and long-term reporting provides granular visibility, including applications and devices in use, websites visited, and volumes of traffic generated. This enables CSPs to analyze user behavior and direct resources toward more profitable revenue plans. Likewise, enterprises can use granular visibility to govern application performance and enforce SLAs according to business priorities.
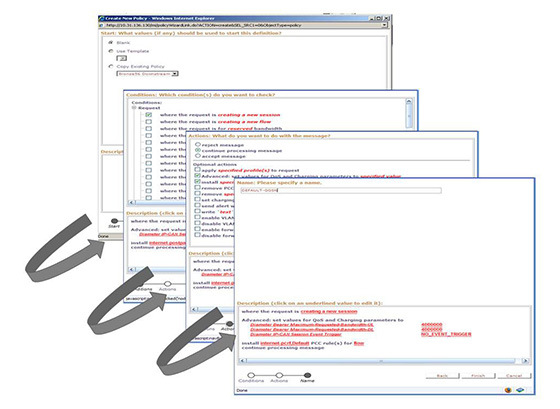
Innovative and Robust Policy Control
Independent policy control provides configurable flexibility, geo-redundant reliability, telco-grade performance, and innovative feature functionality for CSPs of all sizes and market segments.
Flexible, Fast Policy Creation
- Configurable platform facilitates deployment of personalized, subscriber-specific policies
- Customizable policy creation and subscriber-management environment enables network service differentiation
- Integrated policy analytics provides valuable network and subscriber intelligence feedback